Introduction
Cybersecurity is entering a critical turning point. The rise of quantum computing is no longer theoretical; it is steadily progressing toward real-world impact. While today’s encryption standards protect global data, future quantum machines may be capable of breaking them.
This is where post-quantum cybersecurity becomes essential.
Organisations, governments, and individuals must now begin preparing to protect sensitive data from future quantum threats. This article provides a clear, factual, and up-to-date overview of post-quantum cybersecurity, why it matters, and what actions should be taken today.
What Is Post-Quantum Cybersecurity?
Post-quantum cybersecurity refers to cryptographic systems designed to remain secure even against quantum computers.
Today’s encryption methods such as RSA and ECC are based on mathematical problems that classical computers cannot efficiently solve. However, quantum computers use different principles (like superposition and entanglement) that could potentially break these systems.
The key risk: a sufficiently powerful quantum computer could decrypt sensitive data in minutes that would otherwise take classical computers thousands of years.
Why This Is a Real Threat (Not Hype)
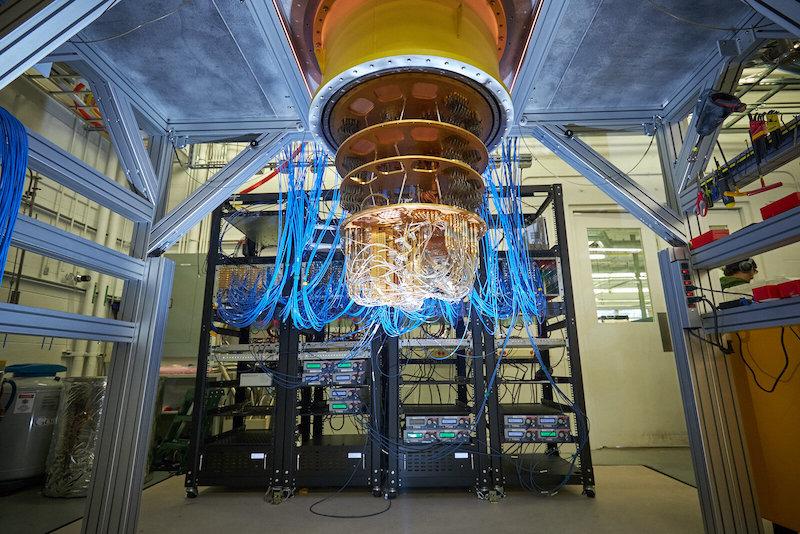
1. Quantum Progress Is Accelerating
Major companies and research institutions are actively building quantum systems. While current machines are limited, steady improvements are being made in:
- Qubit stability
- Error correction
- Scalability
2. “Harvest Now, Decrypt Later” Attacks
Attackers can already:
- Steal encrypted data today
- Store it
- Decrypt it later when quantum computers become powerful enough
This is especially dangerous for:
- Financial data
- Government secrets
- Healthcare records
- Intellectual property
3. Long-Term Data Risk
Any data that needs to remain secure for 5–20 years is already at risk today.
Current Encryption vs Quantum Threat
| Encryption Type | Used Today | Quantum Risk |
|---|---|---|
| RSA | Yes | High |
| ECC | Yes | High |
| AES (Symmetric) | Yes | Moderate (needs larger keys) |
Quantum algorithms like Shor’s Algorithm can break RSA and ECC efficiently once large-scale quantum computers exist.
What Is Post-Quantum Cryptography (PQC)?
Post-Quantum Cryptography (PQC) uses mathematical problems that are believed to be resistant to quantum attacks.
Common PQC approaches:
- Lattice-based cryptography
- Hash-based cryptography
- Code-based cryptography
- Multivariate cryptography
These are being developed and tested globally.
Global Developments (Real & Verified)
1. NIST Standardization (USA)
The National Institute of Standards and Technology (NIST) has been leading efforts to standardise quantum-resistant algorithms.

In recent updates:
- Several algorithms have been selected for future encryption standards
- Organizations are being encouraged to begin migration planning
2. Government Warnings
Multiple governments have issued alerts. urging:
- Early adoption planning
- Risk assessments for quantum exposure
- Transition roadmaps
3. Industry Adoption Begins
Tech companies and cybersecurity firms are:
- Testing hybrid encryption (classical + PQC)
- Updating infrastructure
- Preparing software libraries
Industries Most at Risk
1. Banking & Finance
- Payment systems
- Secure transactions
- Customer data
2. Healthcare
- Patient records
- Medical research data
3. Government & Defense
- Classified communications
- National security systems
4. Cloud & Tech Platforms
- Data storage
- APIs
- Authentication systems
What Businesses Should Do Now
1. Start Crypto Inventory
Identify where encryption is used:
- Applications
- Databases
- APIs
- Network protocols
2. Assess Risk Exposure
Focus on:
- Long-term sensitive data
- External communications
- Legacy systems
3. Adopt Hybrid Cryptography
Use:
- Traditional encryption + quantum-resistant algorithms
This ensures backward compatibility while preparing for the future.
4. Monitor Standards
Stay updated with:
- NIST PQC releases
- Industry frameworks
5. Plan Gradual Migration
Do NOT wait until quantum computers are fully ready. Migration takes years.
Challenges in Post-Quantum Transition
1. Performance Overhead
PQC algorithms often:
- Require larger keys
- Consume more bandwidth
2. Compatibility Issues
Legacy systems may not support:
- New cryptographic libraries
- Updated protocols
3. Lack of Awareness
Many organisations:
- Underestimate the timeline
- Delay preparation
Timeline: When Will Quantum Threat Become Real?
There is no exact date, but expert consensus suggests:
- Short-term (0–5 years): Preparation phase
- Mid-term (5–10 years): Early quantum advantage
- Long-term (10–20 years): Real threat to current encryption
However, preparation must start now, not later.
Key Takeaways
- Quantum computing poses a real future threat to current encryption
- Data stolen today can be decrypted later
- Post-quantum cryptography is already being developed and standardized
- Businesses must begin planning migration immediately
- Waiting increases long-term risk
Conclusion
Post-quantum cybersecurity is not a distant concern—it is a present-day responsibility. Companies that act early will be better positioned to protect their data, maintain trust, and avoid future disruptions.
The transition will take time, resources, and planning. But the cost of inaction could be far greater.